
Quantum computing stands out as a potential game-changer in today’s fast-paced world of technology, where new developments are constantly being introduced. It offers a novel approach to the problem of data protection. Consider the following: traditional computers perform their tasks using 0s and 1s, much like an attentive clerk flicking through paperwork. However, because of quantum physics, quantum computers operate on a whole other level than traditional computers.
They employ qubits, which are able to exist in a variety of states at the same time, rather than dealing with bits. It is the equivalent of having a super helper who can handle numerous tasks at once. This one-of-a-kind quality of quantum computing is going to cause a commotion, particularly with regard to the protection of our vital information from the ever-evolving dangers posed by the internet.
Quantum Encryption
Now, let’s speak about the significant leap forward in cryptography that quantum computing represents. Imagine if the lock protecting your data is one that has many keys, each of which can be in a different state at the same time. Quantum encryption, a ground-breaking method for maintaining the confidentiality of information, works just like this. According to a recent study conducted by ExpressVPN that focused on VPN download and encryption, the older encryption methods relied on mathematical problems that are so complex that standard computers are unable to solve them.
It’s like attempting to solve an extremely challenging problem when you don’t have a picture to guide you. However, quantum computers, which are capable of handling multiple possibilities at the same time, might break these codes far more quickly than the speediest ordinary computers. On the other side, quantum cryptography also offers a solution in the form of the use of quantum physics to the generation of unbreakable codes.
This issue with quantum key distribution includes passing qubits between parties, and if there were any attempts to tamper with them, everyone who was engaged would be made aware of it. It’s like if you’re attempting to listen in on a conversation where the act of listening itself alters what’s being said. The use of the enchantment of quantum physics in the continuous battle for digital security paves the way for quantum encryption, which promises to build an impenetrable wall to protect our vital information.
Quantum Supremacy
Quantum supremacy is a word that may sound like it was taken from a science fiction movie, but it is, in fact, an actual concept. This potential for quantum supremacy is one of the most fascinating aspects of quantum computing. The term “quantum supremacy” refers to the ability of a quantum computer to perform an action that is nearly hard for traditional computers to replicate. When Google announced in 2019 that it had achieved quantum supremacy with its Sycamore quantum computer, the announcement received a lot of attention.
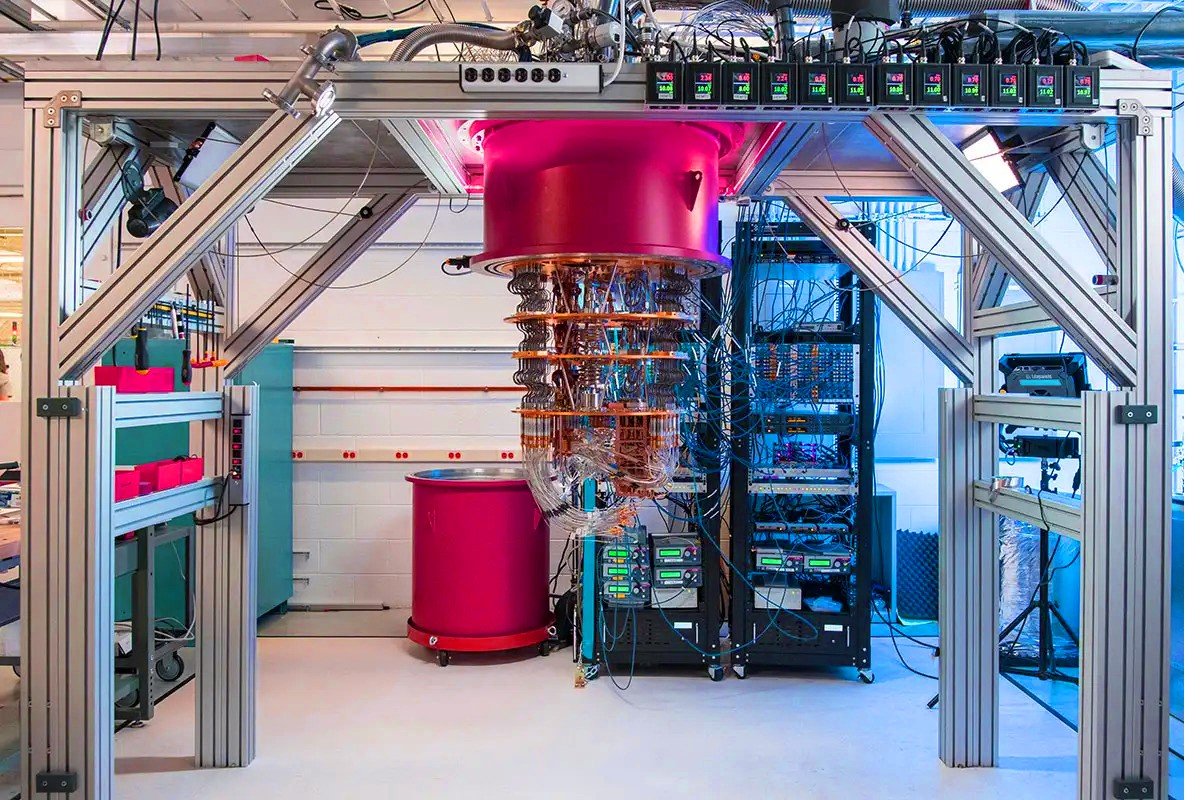
It was able to tackle a particular issue far quicker than even the most powerful conventional supercomputers. We do not yet know how quantum supremacy will affect day-to-day computing, but it has the potential to cause a significant shakeup in the industry. Quantum computers have the potential to revolutionize a wide range of sectors by providing lightning-fast answers to a variety of questions.
These questions range from recreating the tiniest structures for the purpose of developing novel medications to coordinating complex activities. In terms of how rapidly it can calculate, it’s like moving from a bike to a super-fast plane; it’s a significant jump that has the potential to transform the way we utilize technology.
Read More: Review: Quantum NDX-8d Deduplication Appliance
Challenges and Ethical Considerations
The field of quantum computing, despite its potential allure, is not without its share of challenges. As we venture farther into the realm of quantum physics, we will inevitably come face to face with a number of problems and ethical concerns.
Existing cryptography systems face the possibility of being compromised by quantum computers, which is one of the most critical challenges. The immense power of these quantum machines can render obsolete the conventional approaches that are now used to keep data safe. As we get closer to a future dominated by quantum computing, we must design encryption that is robust enough to survive the capabilities of quantum computers. It is analogous to installing a more sophisticated lock on your front door so that it can survive an opponent who is both more intelligent and more powerful.
In addition, the enormous processing power of quantum computers raises worries about their potential for abuse, particularly in the context of decrypting material meant to be kept confidential. To walk a tightrope between utilizing the capability of quantum computing for the benefit of society while at the same time protecting against any possible dangers that may arise is a challenge. It is the same as having a strong instrument that is capable of doing wonderful things but making sure that it is used appropriately in order to avoid unforeseen effects.
Concerning the repercussions of quantum technology on a global scale, there is also the matter of ethics to take into account. How can we guarantee that everyone has an equal opportunity to use this potent tool? Will certain entities use quantum capabilities for their benefit, perhaps causing new imbalances in the digital landscape? These concerns call for thoughtful deliberation and the establishment of ethical frameworks to direct the development and implementation of quantum computing responsibly.
Wrap-Up (The Impact of Quantum Computing on Data Security)
As we draw to a close on our examination of quantum computing, it is abundantly evident that we are stepping into a new age that is fraught with both promise and difficulty. Utilizing the one-of-a-kind qualities of quantum physics, the new method of encryption known as quantum cryptography offers a different way to protect our digital existence. However, the path into quantum supremacy and the possible transformation in a number of different industries must be approached with prudence if it is to be successful.
In light of the fact that we are currently on the verge of entering this quantum frontier, it is of the utmost importance that we maintain vigilance and confront the difficulties that come along with the territory. Responsibly embracing the quantum revolution requires a number of important steps, including the creation of encryption techniques that are resistant to quantum computing, the negotiation of relevant ethical concerns, and the guaranteeing of equal access to this game-changing technology.
The advent of quantum computing carries with it the extraordinary possibility of pushing the limits of what is now imaginable in technological advancement. However, as we go into this unknown region, the responsibility of managing the ethical and practical ramifications that come with such revolutionary ability comes hand in hand with the joy of experiencing quantum progress. It is an exciting yet measured time in the constantly developing world of technology, and the decisions that we make right now will determine the path that the quantum future takes.
Read More: New AI Program Creates Realistic ‘ Talking Heads’-Creepy or Cool?











