In this article, we’ll explore how to safely use untrusted shortcuts on iOS 13 (2023). Shortcuts on iOS devices allow users to automate tasks and create custom actions. However, not all shortcuts are trustworthy, and installing untrusted shortcuts can pose a security risk.

- Explanation of shortcuts and their benefits
- The potential security risks of using untrusted shortcuts
- The importance of being cautious when installing untrusted shortcuts.
Read More: How to Convert articles into podcasts for free with Podcastle AI (2023)
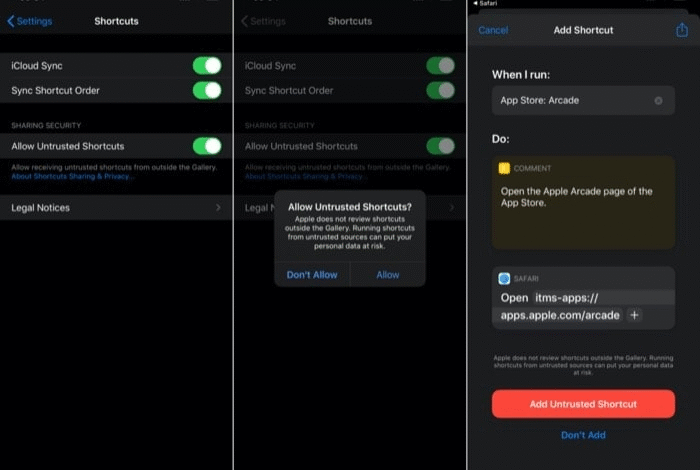
How to Download and Install Untrusted Shortcuts
- Overview of how to download untrusted shortcuts from third-party sources
- Explanation of the potential security risks of installing untrusted shortcuts
- How to check the permissions required by a shortcut before installing it
- How to install and use untrusted shortcuts in a safe manner
How to Determine If a Shortcut Is Trustworthy
- Explanation of how to check the reputation of a shortcut
- The importance of reading reviews and ratings before installing a shortcut
- How to find out if a shortcut has been reported as malicious
- How to use VirusTotal to scan a shortcut for malware
Best Practices for Using Untrusted Shortcuts
- How to keep your iOS device secure while using untrusted shortcuts
- Explanation of the importance of keeping your iOS device updated
- How to back up your iOS device before installing untrusted shortcuts
- How to revoke shortcut permissions if necessary
- The importance of being vigilant and cautious when using untrusted shortcuts.
Benefits of Using Untrusted Shortcuts
Access to a Wider Range of Shortcuts
One of the primary benefits of using untrusted shortcuts is the ability to access a wider range of shortcuts. Trusted shortcuts are only available from a limited number of sources, such as the App Store or the Shortcuts Gallery. By allowing untrusted shortcuts, you can access shortcuts created by individuals or small groups that may not have the resources or inclination to have their shortcuts vetted by Apple.
Personalized Shortcuts
Another benefit of using shortcuts is the ability to create personalized shortcuts tailored to your specific needs. For example, you may have a workflow that requires you to access a specific website and copy a piece of information. With untrusted shortcuts, you can create a shortcut that automates this process, saving you time and effort.
Increased Flexibility
shortcuts also provide increased flexibility in how you use your iOS device. With trusted shortcuts, you are limited to the actions and workflows provided by Apple or the source of the trusted shortcut. With shortcuts, you can create custom workflows and actions that meet your specific needs. This can lead to increased efficiency and productivity.
Enhanced Privacy
When you use a trusted shortcut, you are trusting that the source of the shortcut will not collect or misuse your data. While Apple does vet trusted shortcuts to ensure they meet certain privacy and security standards, there is always a risk that your data could be misused. With shortcuts, you can carefully review the actions and workflows of the shortcut before allowing it to run. This can provide an additional layer of privacy and security.
Improved Learning Opportunities
Finally, using shortcuts can provide an excellent learning opportunity. By exploring the actions and workflows of shortcuts, you can gain a better understanding of how shortcuts work and how you can create your own. This can lead to increased creativity and innovation in how you use your iOS device.
Read More: Best Google Docs Keyboard Shortcuts for PC and Mac
Conclusion
Using these shortcuts on iOS 13 can be risky but it is possible to do so safely by taking certain precautions. Checking the source, reading reviews and ratings, avoiding giving full access, and limiting the shortcut’s capabilities are all important steps to take when using untrusted shortcuts. By following these guidelines, you can enjoy the benefits of using shortcuts while protecting your data and your device. Remember to always exercise caution and be mindful of the potential risks when using untrusted shortcuts on your iOS device.
FAQs
- Can untrusted shortcuts damage my iOS device?
Yes, untrusted shortcuts have the potential to damage your iOS device by accessing sensitive information or executing malicious code. It’s essential to be cautious when installing untrusted shortcuts and to check their permissions and reputation before using them.
- How can I tell if a shortcut is safe to use?
You can determine if a shortcut is safe to use by checking its reputation, reading reviews and ratings, and scanning it for malware using tools like VirusTotal. It’s also crucial to be cautious when installing shortcuts from third-party sources and to only install those that come from trusted sources.
- Is it possible to modify a shortcut to make it safe to use?
It’s possible to modify a shortcut to make it safer to use by removing any potentially malicious code or limiting its permissions. However, this requires technical expertise, and it’s generally recommended to only install trusted shortcuts from reputable sources.
- What should I do if I accidentally install a malicious shortcut?
If you accidentally install a malicious shortcut, you should remove it immediately and revoke its permissions. You should also scan your device for malware and change any passwords or sensitive information that the shortcut may have accessed.
- Are there any trusted sources for downloading shortcuts?
Yes, there are several trusted sources for downloading shortcuts, including the official Apple Shortcuts Gallery, reputable third-party app stores, and popular online forums dedicated to sharing trusted shortcuts.











