Cybersecurity
-

How Small Businesses Can Stay Safe with Security as a Service?
Small businesses face numerous challenges, including limited resources and budgets, which make it difficult to invest in advanced cybersecurity solutions.…
Read More » -
The Vital Multicloud Security Solutions That’s Keeping Financial Services Firms Safer
In recent years, the financial services industry has experienced a significant increase in cyber threats. These threats range from phishing…
Read More » -

Are Energy and Utility Companies Underestimating the Risk of a Cyberattack?
Energy and utility companies have long been considered critical infrastructure and are essential to modern life. These companies provide the…
Read More » -

Cisco Umbrella Defeats Cyberthreats with Actionable Intelligence
Do you wanr to know how cisco umbrella defeats cyberthreats with actionable intelligence. The world of cybersecurity is constantly evolving,…
Read More » -

Which Security Key You Should Use With Google?
Which Security Key You Should Use With Google? Do you know which security key you should use with google? we…
Read More » -

Girl Scouts Cyber Challenge
Join the Girls Scouts of historic Georgia on an epic cyber challenge adventure as you detect, decode, defend, and more!…
Read More » -

Help Your Kids Understand Cybersecurity
How to Help Your Kids Understand Cybersecurity Every day, almost 1 million cybersecurity attacks occur, and they don’t just target…
Read More » -

Cyber Threat Report: Amazon Prime Phishing Email
Do you know about Amazon Prime Phishing Email? Scammers send emails to potential victims claiming the recipient has begun an…
Read More » -

Cyber Threat Report: Amazon Phishing Email
What do you know about Phishing email from Amazon? Scammers send emails to potential victims claiming the recipient has begun…
Read More » -

Cyber Threat Report: Zoom Security Exploit
Zoom Security Exploit problems plague Zoom, a major provider of video conferencing services. According to Tom Anthony, the Product VP…
Read More » -

Cyber Threat Report: Insider Threats
Insider threats are people that constitute a security risk and have access to the network and data of your business.…
Read More » -
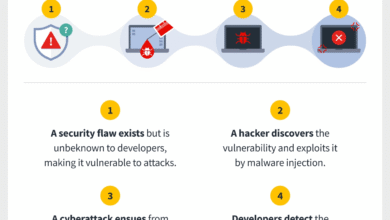
Cyber Threat Report: New Zero-Day Attacks
For all supported versions of its Windows operating system and other devices, Microsoft delivered its August 2020 batch of software…
Read More » -

Cyber Threat Report: SBA COVID-19 Phishing Emails
A counterfeit Small Business Administration (SBA) COVID-19 loan relief portal was the subject of Alert AA20-225A from the Cybersecurity and…
Read More » -

Consider Yourself a Target for Hackers
Consider yourself a target for hackers if you own a computer, smartphone, tablet, or other electronic device. You are a…
Read More » -

Cyber Threat Report: Protect Your Children’s Sensitive Information
It’s not surprising that parents have had to move their children’s activities to digital devices given the decline in social…
Read More » -

Cyber Threat Report: A New Bluetooth Vulnerability
Bluetooth vulnerability in the Cross-Transport Key Derivation (CTKD), which is a component of the Bluetooth standard. When pairing two Bluetooth…
Read More » -

9 Impressive Benefits of Managed IT Services
There are several reasons for this. Let’s look at 9 Benefits of Managed IT Services. Predictable Costs That Are Also…
Read More » -

The Most Common Cyber Threats Faced by a Business (and How to Recognize Them)
So what, exactly, are the Cyber Threats Faced by a Business? And, how can you minimize the risks? This article…
Read More »

