Tech News
-

Girl Scouts Cyber Challenge
Join the Girls Scouts of historic Georgia on an epic cyber challenge adventure as you detect, decode, defend, and more!…
Read More » -

Network Security Solutions for Small to Medium-Sized Businesses
Having a secure network infrastructure is just one of several requirements for operating a business successfully. After their network security…
Read More » -

Help Your Kids Understand Cybersecurity
How to Help Your Kids Understand Cybersecurity Every day, almost 1 million cybersecurity attacks occur, and they don’t just target…
Read More » -

Cyber Threat Report: Amazon Prime Phishing Email
Do you know about Amazon Prime Phishing Email? Scammers send emails to potential victims claiming the recipient has begun an…
Read More » -

Cyber Threat Report: Amazon Phishing Email
What do you know about Phishing email from Amazon? Scammers send emails to potential victims claiming the recipient has begun…
Read More » -

Virtual Engagement Series: Reboot 2020
More and more workers are taking safety precautions by continuing to work remotely from home as the coronavirus spreads. It’s…
Read More » -
First AI robot to speak Arabic is unveiled in Saudi Arabia as “Sara.”
According to a report by the state news agency SPA, Saudi Arabia creates history by unveiling "Sara," the first robot…
Read More » -

Cyber Threat Report: Zoom Security Exploit
Zoom Security Exploit problems plague Zoom, a major provider of video conferencing services. According to Tom Anthony, the Product VP…
Read More » -

Cyber Threat Report: Insider Threats
Insider threats are people that constitute a security risk and have access to the network and data of your business.…
Read More » -
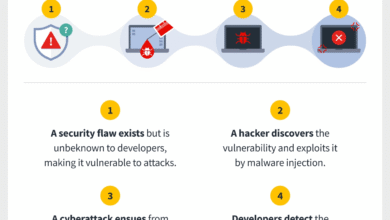
Cyber Threat Report: New Zero-Day Attacks
For all supported versions of its Windows operating system and other devices, Microsoft delivered its August 2020 batch of software…
Read More » -

Cyber Threat Report: SBA COVID-19 Phishing Emails
A counterfeit Small Business Administration (SBA) COVID-19 loan relief portal was the subject of Alert AA20-225A from the Cybersecurity and…
Read More » -

Consider Yourself a Target for Hackers
Consider yourself a target for hackers if you own a computer, smartphone, tablet, or other electronic device. You are a…
Read More » -

What You Need to Know About ‘Juice Jacking’
What does “Juice Jacking” mean? Juice Jacking is the practice of criminals placing malware on cables and/or public charging stations…
Read More » -
Hidden Tricks Inside Windows 10
SILENT NOTIFICATIONS Use Windows 10 Focus Assist to muffle those bothersome notifications. Navigate to Settings, select System, and then choose…
Read More » -

Can You Get A Loan For Online Store Without Having Your Credit Checked?
You may want Loan For Online Store if you want to start a new internet business or introduce a new…
Read More » -

Google Chrome with New Beta Version has Improved Picture-in-Picture.
According to The Verge, Google is working on a new Chrome beta, version 111, which will have a document picture-in-picture…
Read More »